Endpoint Security
Solutions
|Protect Your Business
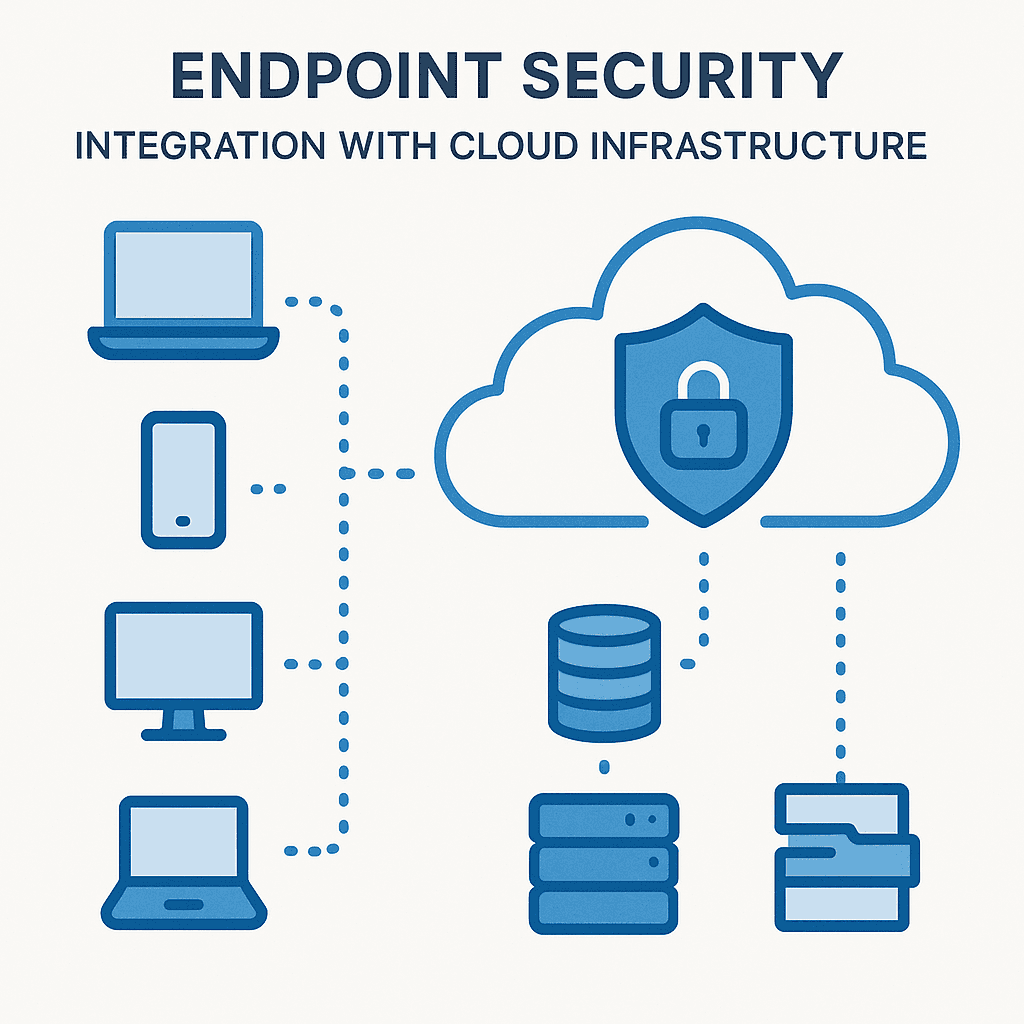
Stop Cyber Threats with Robust Endpoint Security Solutions
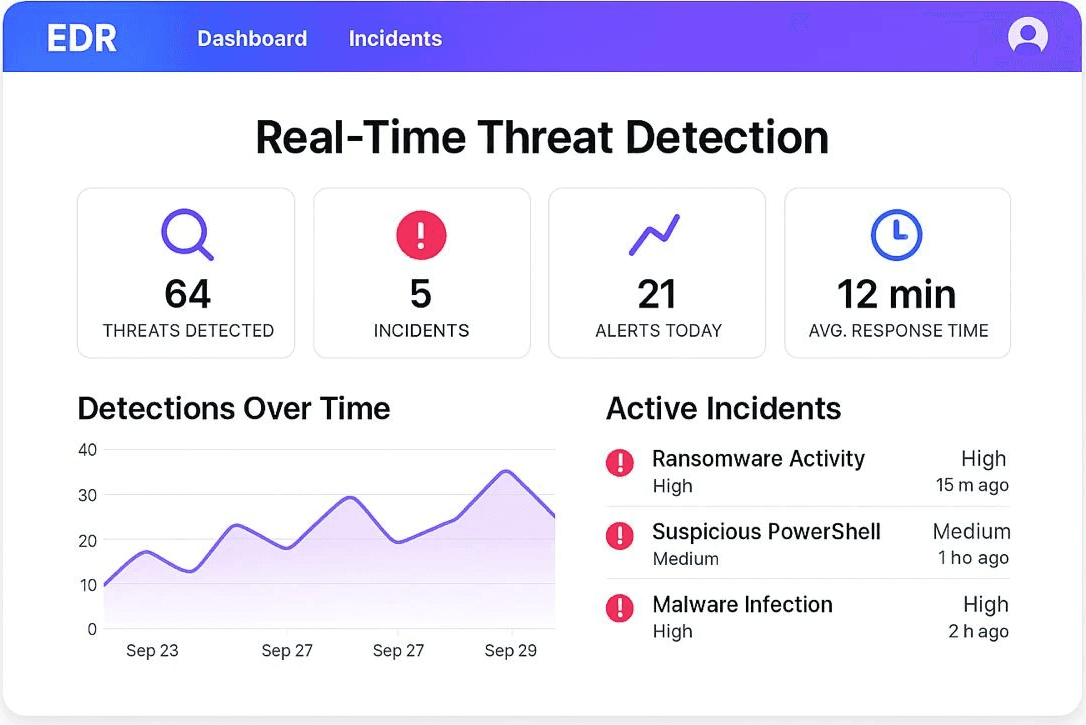
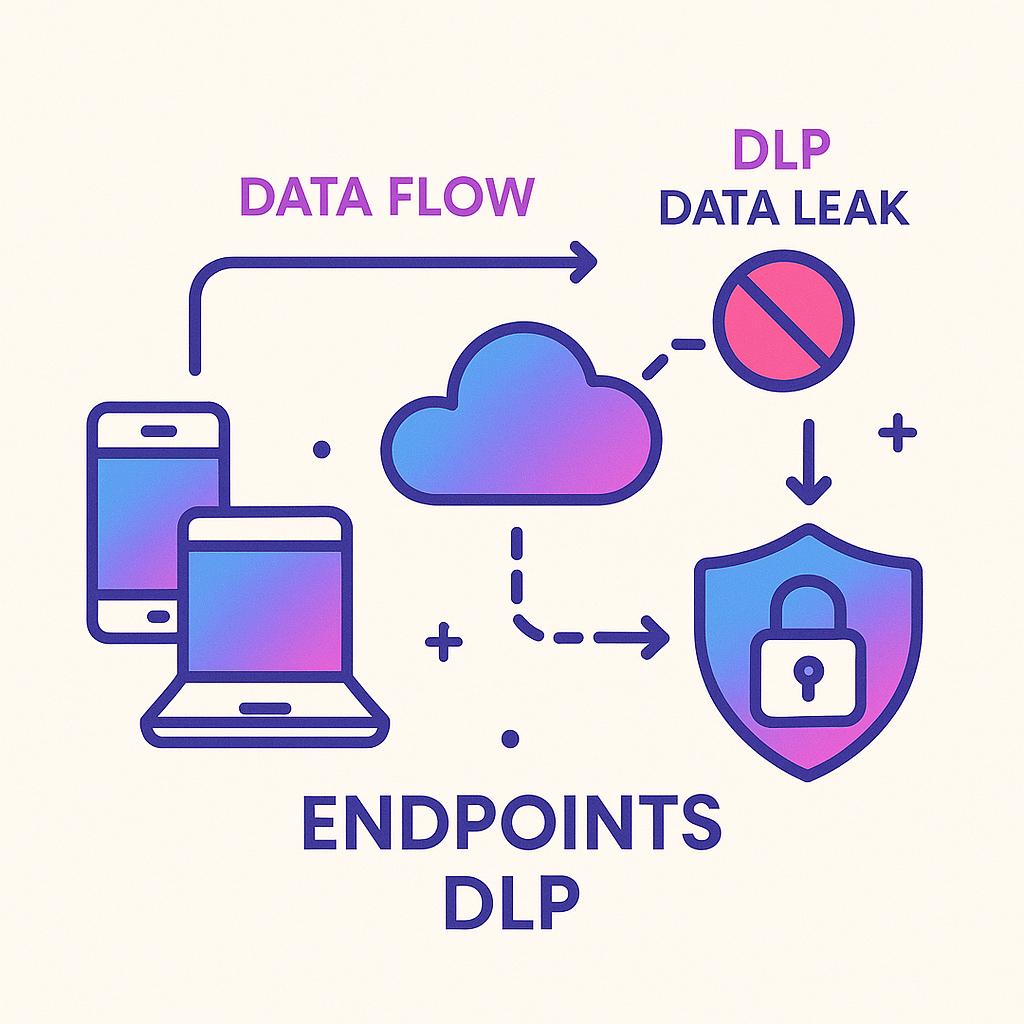
In today's digital landscape, your endpoints are the frontline of defense against evolving cyber threats. Are your laptops, desktops, servers, and mobile devices adequately protected? A single compromised endpoint can expose your entire organization to data breaches, financial losses, and reputational damage. Aadit Technologies provides comprehensive endpoint security solutions designed to proactively defend your business from sophisticated attacks, ensuring business continuity and data protection. We specialize in delivering cutting-edge endpoint security solutions tailored to meet the unique needs of your organization. From cloud-based solutions to on-premise deployments, we help you create a secure environment that safeguards your sensitive data and ensures compliance with industry regulations. Get a free consultation today and discover how we can fortify your defenses.
Get a free consultation today and discover how we can fortify your defenses